Hackers use stolen emails from a chain of answers in a wave of phishing attacks targeting IKEA employees.
IKEA-targeted cyber-attacks
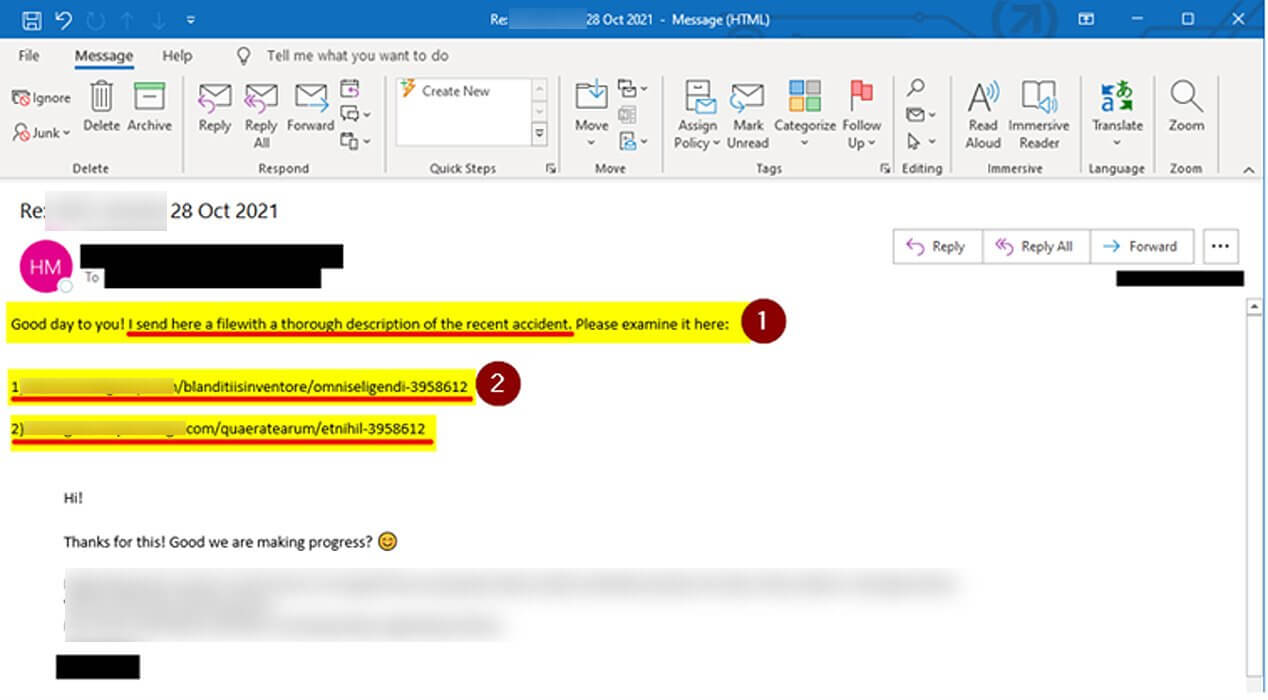
According to the BleepingComputer publication, the company has begun informing its employees in a group of internal emails about the new phishing attacks of the answer chain where IKEA’s internal mailboxes are targets. According to the company’s emails to employees, these appear to be filled with seven-digit links. The IKEA IT team also advised employees not to open the emails and report them immediately to the IT department.
There is currently no confirmation if internal servers have been compromised.
There is an ongoing cyber attack targeting Inter IKEA mailboxes. Other IKEA organizations, suppliers and business partners are affected by this attack and distribute more malicious emails to people at Inter IKEA. (…) This means that the attack can come via email from someone you work with, from any external organization, and in response to an ongoing conversation. It is therefore difficult to identify, which is why we ask you to be especially careful.
BleepingComputer also mentions that the publication was able to identify Ikea’s cyber attack that addresses this with the URL that can be found in the body of the emails. It seems that if someone clicks on the provided URL, they will be directed to download a charts.zip file. Inside this zip file, there is a damaged Excel document. In order to view it, users must enable the ‘Enable Content’ or ‘Enable Editing’ option. Pressing these buttons will only result in malicious macros. These macros have the function of downloading from a remote site a number of files called ‘bestb.ocx’, ‘besta.ocx’ or ‘bestc.ocx’ and then these will be saved in the C: Datop folder.
OCX files are basically ActiveX controls that have been deprecated and renamed and the installation of the malware load occurs after they are executed using the regsvr32.exe command. The ad also mentions that campaigns using Trojan Qbot and possibly Emotet have used the same method as it is currently used in this Ikea campaign.
What is a chain reaction?
In these types of cyberattacks, cybercriminals usually commit the theft of legitimate corporate emails. The next thing is that they reply to these emails with messages containing damaged links. When this link is opened, the malware is deployed on the host device. These are legitimate emails from an organization so that recipients will not question their credibility, making them an effective phishing program.
How can Heimdal ™ protect you?
Heimdal ™ always has the most effective solutions ready to help secure your organization’s critical infrastructure. You can use tools like email security and email fraud prevention. The first protects against e-mail threats and supply chain attacks by combining proprietary mail threat prevention and Office 365 support, the second eliminates Business Email Compromise (BEC), CEO fraud and impersonation through its 125 vectors.
Did you enjoy this article? Follow us on LinkedIn, Twitter, Facebook, YouTube, Or Instagram Keep up to date with everything we publish!

